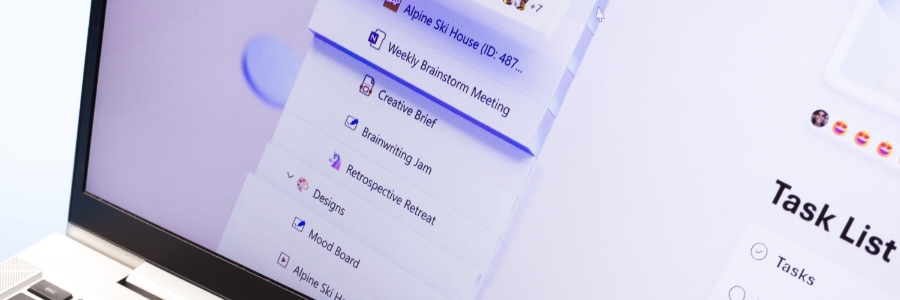
More and more businesses are leveraging data dashboards. These business intelligence tools can visualize data, giving businesses a comprehensive snapshot of their performance in various areas, including marketing and finance. Let’s take a closer look at how dashboards can support various business activities. Marketing Marketing professionals analyze vast amounts of data from multiple sources. With… Continue reading How businesses can benefit from dashboards
How businesses can benefit from dashboards