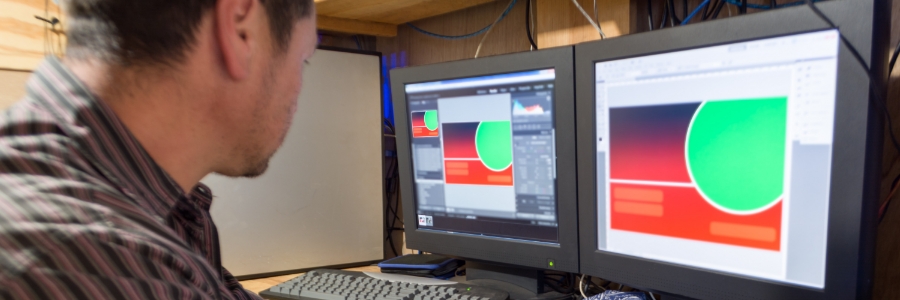
If you’re like most business owners, you’re always looking for ways to improve your employees’ productivity. One way to do this is by upgrading your office computers with dual monitor systems. Here are the benefits of using two monitors per desktop and how this setup can help your business achieve its goals. Efficient multitasking and… Continue reading Use dual monitor systems for improved productivity
Use dual monitor systems for improved productivity