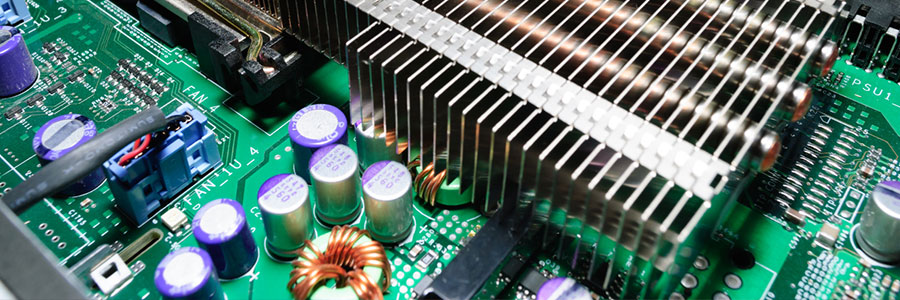
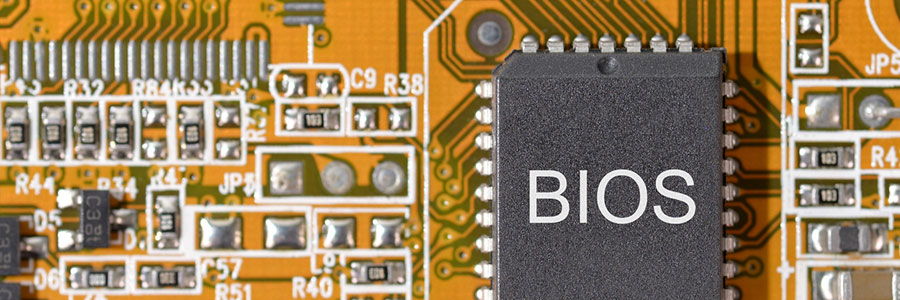
For decades, one of the most foundational principles of cyber security has remained the same: Always update and patch your software. But for most people, hardware is exempt from this process. They think of hardware as nothing more than a vessel for software to occupy — and that’s totally incorrect. Read on to learn more… Continue reading Firmware: the threat most users overlook
Firmware: the threat most users overlook